Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation is a valuable resource designed to help individuals protect their systems, data, and identities from AI-powered threats. With the increasing sophistication of artificial intelligence (AI), cybercriminals are developing more advanced methods to exploit its capabilities, making it imperative to stay informed about the latest AI spoofing techniques.
Editor's Notes: "Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation" has published today date". This is a must-read resource for cybersecurity professionals, IT managers, and anyone concerned about the potential risks associated with AI spoofing.
After extensive analysis, digging information, made Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation, we put together this Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation guide to help target audience make the right decision.
The table below provides a summary of the key differences between AI spoofing and traditional cyberattacks.
| Characteristic | Tradtional Cyberattacks | AI spoofing |
|---|---|---|
| Method | Rely on human actors to carry out attacks, using techniques such as phishing, malware, and SQL injection | Leverage AI algorithms to automate attacks, making them more efficient and difficult to detect |
| Target | Typically target specific individuals or organizations | Can target a wide range of targets, including individuals, organizations, and infrastructures |
| Damage | Can cause a variety of damage, including data theft, financial loss, and reputational damage | Can have devastating consequences, including the disruption of critical infrastructure, financial collapse, and loss of lif |
Transition to main article topics
FAQ
This FAQ section addresses common queries and misconceptions regarding AI spoofing, aiming to provide clarity and enhance understanding of this crucial topic.

The Comprehensive Guide to Agile Methodology - Golden Technology - Source goldenitinc.com
Q1: What is AI spoofing, and why is it a crucial concern?
AI spoofing denotes the malicious manipulation of AI systems to deceive or mislead users. Perpetrators exploit vulnerabilities in AI algorithms or infrastructure to generate deceptive content, impersonate legitimate entities, or compromise sensitive information. AI spoofing poses significant risks to individuals, organizations, and society as a whole.
Q2: How can I identify Potential AI spoofing attempts?
Several indicators may suggest potential AI spoofing attempts: inconsistencies in content, unnatural behavior or language patterns, implausible or sensational claims, and attempts to bypass security measures. Maintaining vigilance and employing robust detection tools is essential for safeguarding against AI spoofing.
Q3: What are the effective mitigation strategies against AI spoofing?
Implementing multi-layered defense mechanisms, leveraging advanced detection algorithms, fostering user awareness, and establishing clear reporting channels can effectively mitigate AI spoofing. A comprehensive approach involving stakeholders from technical, security, and regulatory backgrounds is crucial.
Q4: How does AI spoofing impact different industries and sectors?
AI spoofing has far-reaching consequences across sectors, including finance, healthcare, critical infrastructure, and social media. Fraudulent transactions, misinformation campaigns, and compromised patient data are just a few examples of the potential threats posed by AI spoofing.
Q5: What are the legal and ethical implications of AI spoofing?
AI spoofing raises significant legal and ethical concerns. Misuse of AI systems can lead to criminal prosecution, reputational damage, and erosion of trust in AI technology. Establishing clear regulations and ethical guidelines is essential for responsible AI development and deployment.
Q6: How can we foster collaboration in addressing AI spoofing?
Collaboration among researchers, industry experts, law enforcement agencies, and policymakers is imperative for addressing AI spoofing. Sharing knowledge, best practices, and resources can enhance detection capabilities and promote effective mitigation strategies.
By understanding the nature of AI spoofing, identifying its potential indicators, and implementing robust mitigation strategies, we can safeguard against its malicious consequences and foster a future where AI technology is used responsibly and ethically.
Continue to the next section for an in-depth analysis of AI spoofing detection techniques.
Tips
In order to detect and mitigate AI spoofing, there are a few suggested tips.
Tip 1: Utilize Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation detection tools. These tools can help identify suspicious activity and flag potential spoofing attempts.
Tip 2: Implement strong authentication measures. This will help prevent unauthorized access to your AI systems and data.
Tip 3: Monitor your AI systems for suspicious activity. This will help you identify any potential spoofing attempts and take appropriate action.
Tip 4: Educate your users about AI spoofing. This will help them recognize potential spoofing attempts and report them to you.
Tip 5: Stay up-to-date on the latest AI spoofing techniques. This will help you stay ahead of the curve and protect your AI systems from the latest threats.
These are just a few tips to help you detect and mitigate AI spoofing. By following these tips, you can help protect your AI systems and data from this growing threat.
For more information, please refer to the full article: Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation
Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation
Artificial intelligence (AI) spoofing poses a significant threat to various industries, requiring a comprehensive understanding of its detection and mitigation strategies. This guide explores six key aspects crucial for uncovering and addressing AI spoofing attempts, providing valuable insights for organizations and individuals.
- Detection Techniques: Identifying spoofing methods through anomaly detection, behavior analysis, and digital fingerprinting.
- Mitigation Strategies: Implementing defense mechanisms such as data encryption, multi-factor authentication, and AI-powered security solutions.
- Behavioral Analysis: Monitoring user actions for deviations from established patterns, such as unusual login times or device behavior.
- Data Integrity: Ensuring data accuracy and consistency to prevent manipulation and spoofing attempts.
- Contextual Awareness: Understanding the context of user interactions to identify suspicious activities that may indicate spoofing.
- Collaboration and Information Sharing: Establishing industry partnerships and sharing threat intelligence to stay informed about emerging spoofing techniques.
By addressing these key aspects, organizations can enhance their ability to detect and mitigate AI spoofing, safeguarding their systems, data, and reputation. Continuous monitoring, adaptation, and collaboration are essential to stay ahead of evolving threats and ensure the integrity of AI-driven systems.

Spoofing - GUIDE GNSS - Source guide-gnss.com
Unveiling AI Spoofing: A Comprehensive Guide For Detection And Mitigation
In the era of artificial intelligence (AI), spoofing techniques have emerged as a significant threat. AI spoofing refers to deceptive practices that attempt to make AI systems or their outputs appear genuine when they are not. This comprehensive guide explores the detection and mitigation of AI spoofing, providing essential insights into the causes and effects of this issue. Real-life examples illustrate the importance of understanding and addressing AI spoofing, emphasizing its practical significance in safeguarding AI systems' integrity and reliability.
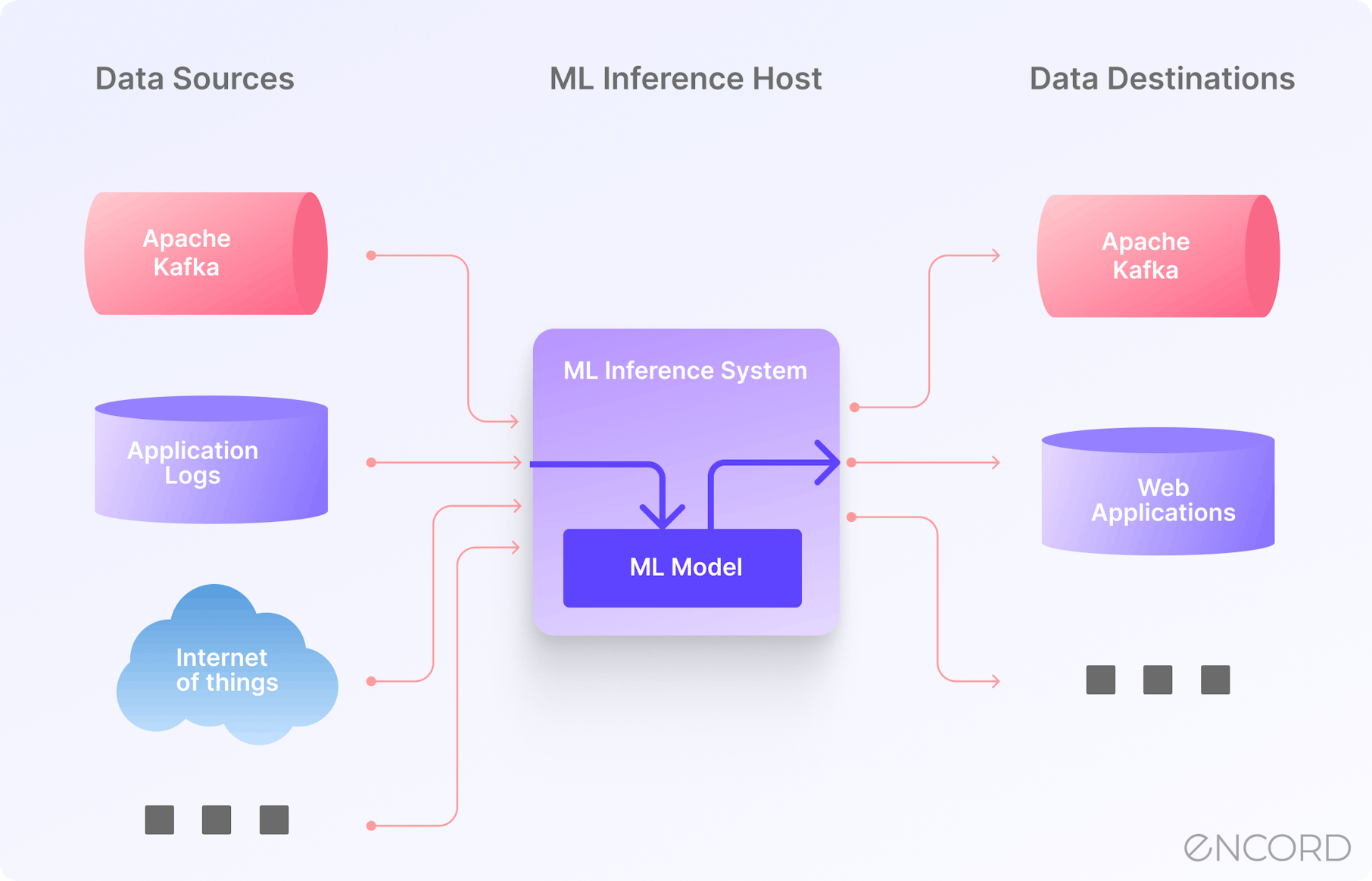
Model Inference in Machine Learning | Encord - Source encord.com
The guide offers a detailed analysis of AI spoofing techniques, including deepfakes, synthetic media, and impersonation attacks. It examines the challenges posed by these techniques and discusses effective countermeasures. The importance of human oversight, robust authentication mechanisms, and continuous monitoring are highlighted as key elements of a comprehensive AI spoofing mitigation strategy.
The guide concludes by emphasizing the ongoing nature of the AI spoofing threat and the need for continued vigilance. It encourages collaboration between researchers, industry practitioners, and policymakers to stay ahead of emerging spoofing techniques and develop effective mitigation strategies. By raising awareness and providing practical guidance, this guide empowers organizations to protect their AI systems from spoofing and ensure their integrity and trustworthiness.
Conclusion
"Unveiling AI Spoofing: A Comprehensive Guide for Detection and Mitigation" provides a roadmap for navigating the challenges of AI spoofing. It emphasizes the importance of understanding the causes and effects of AI spoofing and offers practical guidance for detection and mitigation. By implementing the strategies outlined in this guide, organizations can safeguard their AI systems, protect against reputational damage, and maintain public trust in AI technology.
The fight against AI spoofing is an ongoing effort. As AI technology continues to evolve, so too must our defenses against spoofing. By staying informed about the latest spoofing techniques and sharing best practices, we can stay ahead of the threat and ensure that AI remains a force for good in our world.
Tidak ada komentar:
Write komentar